Web Design 101: Essential Principles for a Seamless User Experience
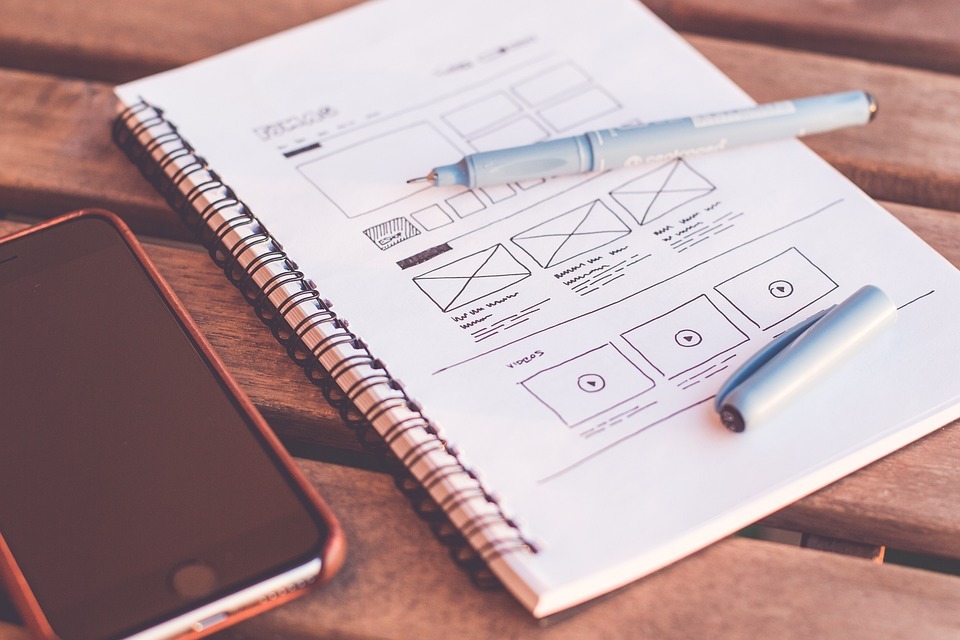
Web Design 101: Essential Principles for a Seamless User Experience In today’s digital age, an appealing and user-friendly website is crucial for the success of any business or organization. Effective web design encompasses various essential principles that improve the overall user experience (UX) and keep visitors engaged. Here, we explore some fundamental principles that will […]
Web Design 101: Essential Principles for a Seamless User Experience Read More »